Podcast Episodes
Back to Search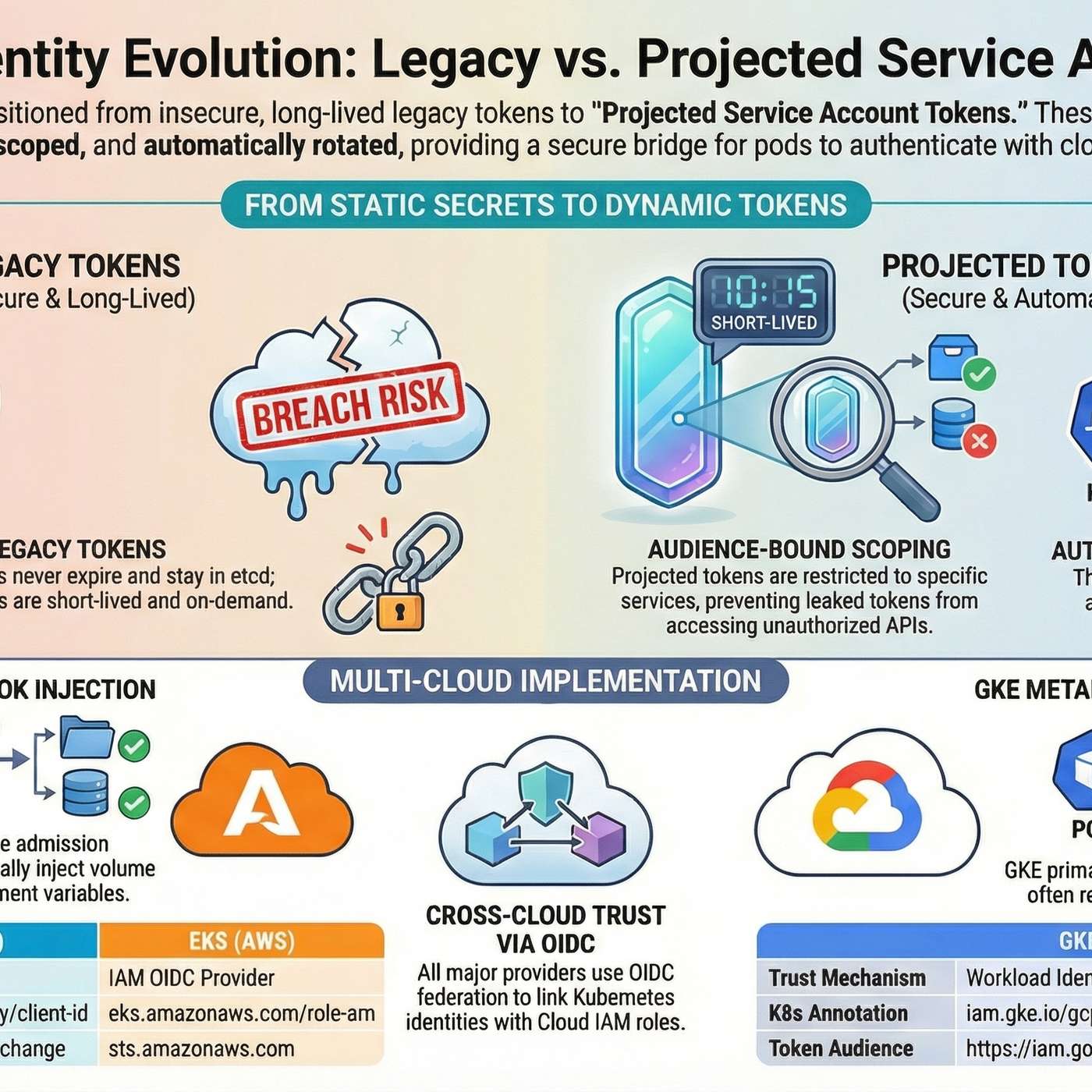
Secure Pod Identity Across Clouds: AKS Workload Identity, EKS IRSA, GKE Workload Identity
This story was originally published on HackerNoon at: https://hackernoon.com/secure-pod-identity-across-clouds-aks-workload-identity-eks-irs…
2 months, 2 weeks ago
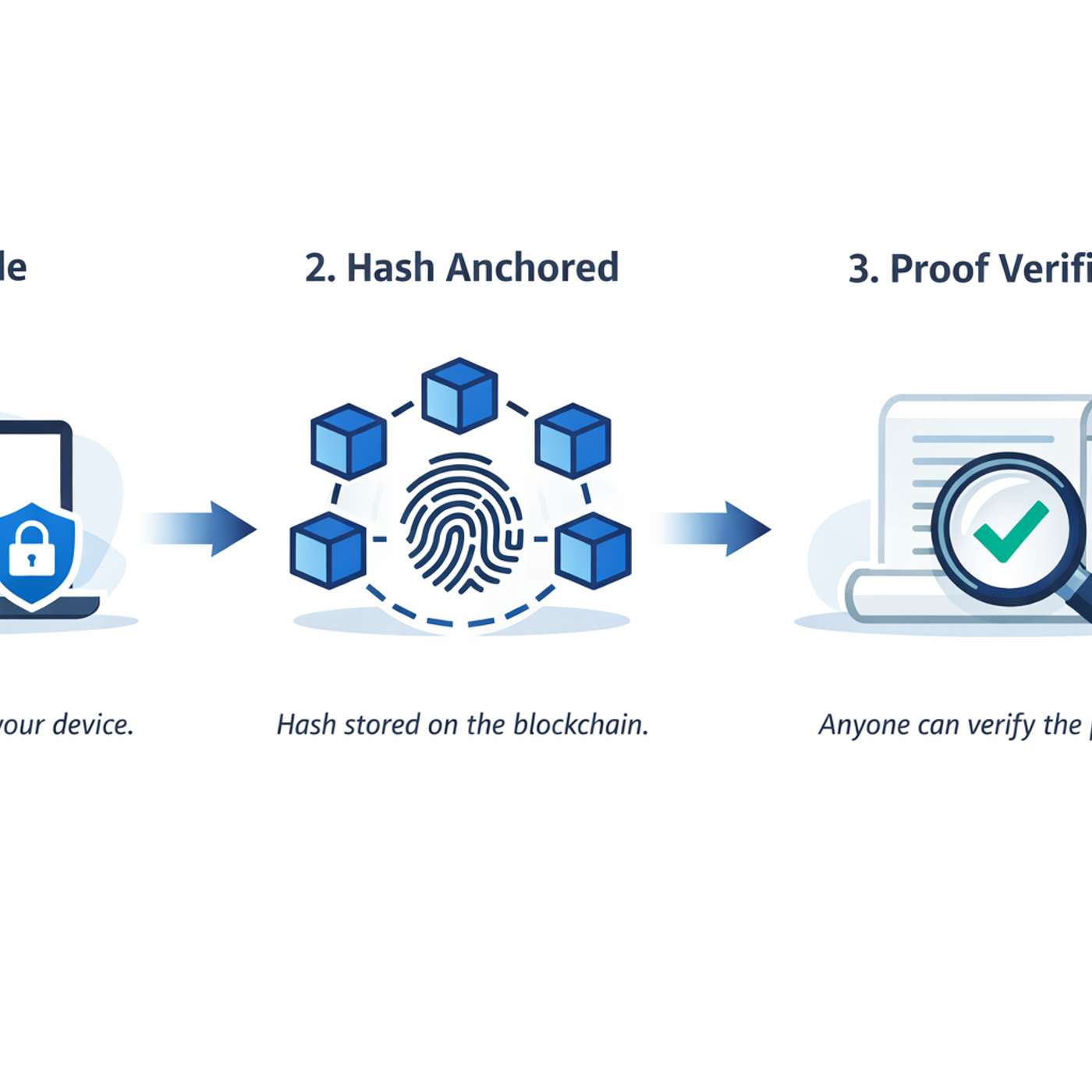
DocProof Lets You Prove a File Existed—Without Uploading the File
This story was originally published on HackerNoon at: https://hackernoon.com/docproof-lets-you-prove-a-file-existedwithout-uploading-the-fil…
2 months, 2 weeks ago
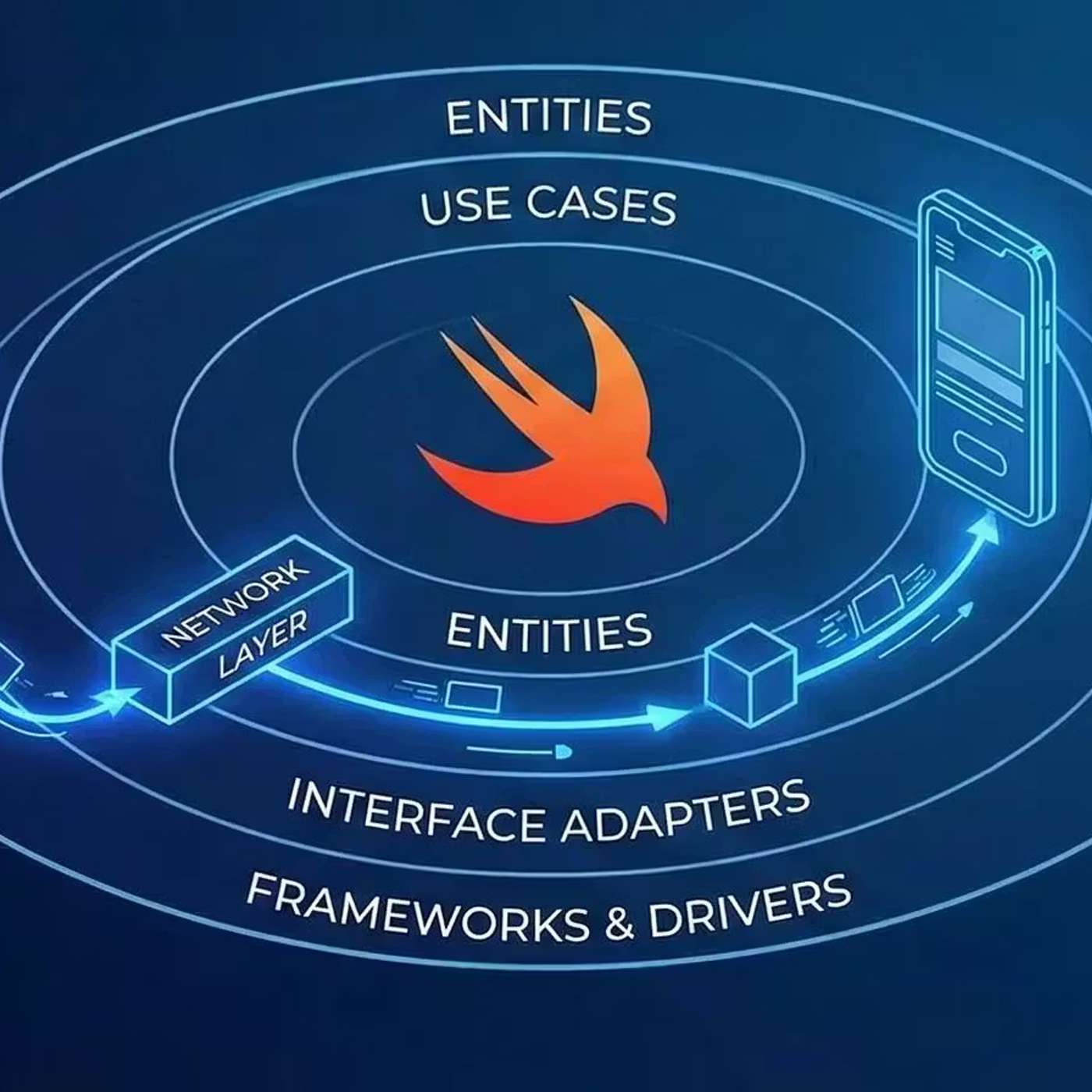
Stop Letting Your iOS Network Layer Become a Junk Drawer
This story was originally published on HackerNoon at: https://hackernoon.com/stop-letting-your-ios-network-layer-become-a-junk-drawer. …
2 months, 2 weeks ago

Infrastructure as Code in Practice: What It Solves — and What It Doesn’t
This story was originally published on HackerNoon at: https://hackernoon.com/infrastructure-as-code-in-practice-what-it-solves-and-what-it-d…
2 months, 2 weeks ago

Why We Stopped Using Single-Activity Architecture Everywhere
This story was originally published on HackerNoon at: https://hackernoon.com/why-we-stopped-using-single-activity-architecture-everywhere. …
2 months, 2 weeks ago
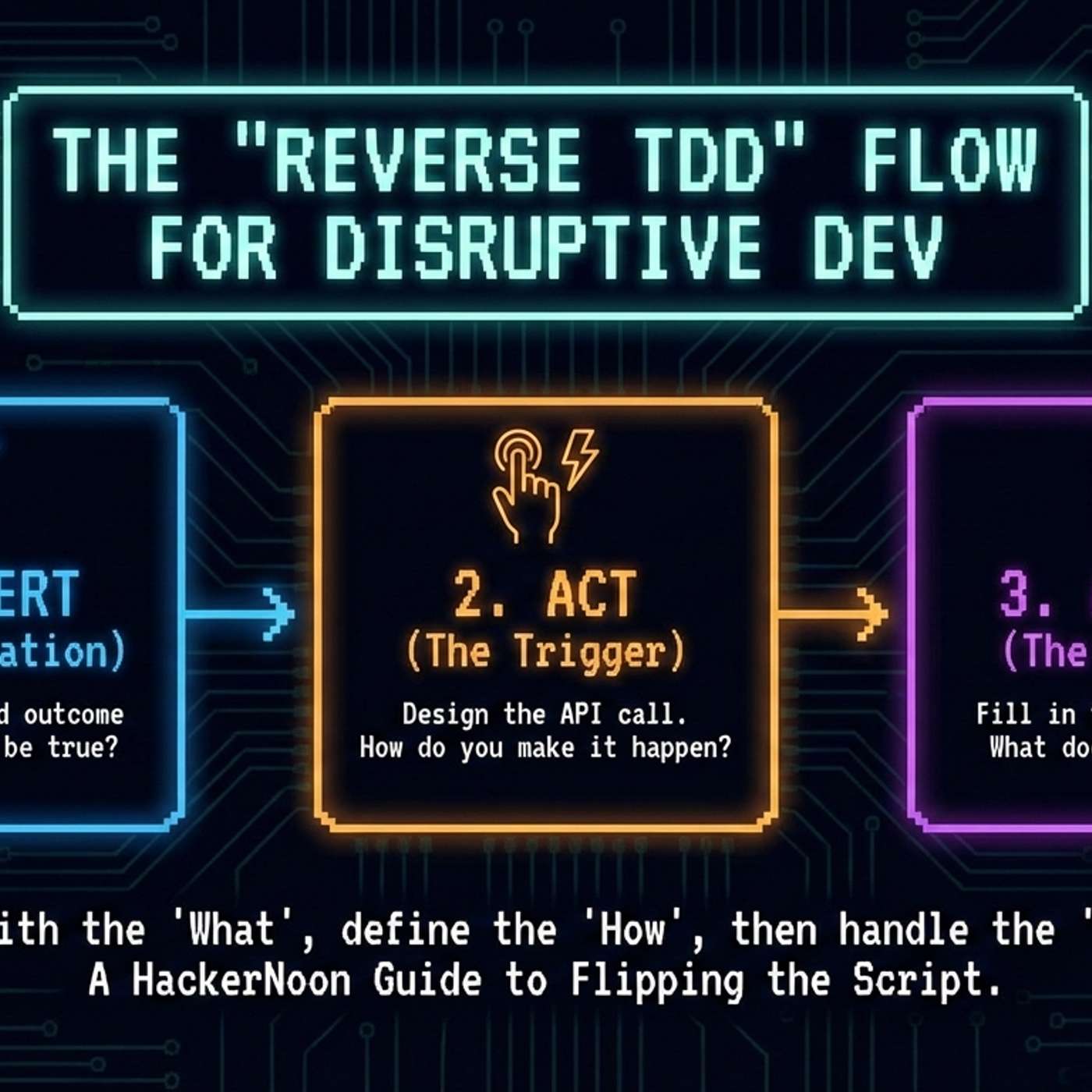
TDD Is Backwards: Why Assertions Should Come First in Disruptive Development
This story was originally published on HackerNoon at: https://hackernoon.com/tdd-is-backwards-why-assertions-should-come-first-in-disruptive…
2 months, 2 weeks ago

From PDFs to Proof Pipelines: Building Audit-Grade Traceability in Regulated Deep-Tech
This story was originally published on HackerNoon at: https://hackernoon.com/from-pdfs-to-proof-pipelines-building-audit-grade-traceability-…
2 months, 2 weeks ago

What You Have to Know About Syntactic Support for Error Handling
This story was originally published on HackerNoon at: https://hackernoon.com/what-you-have-to-know-about-syntactic-support-for-error-handlin…
2 months, 2 weeks ago

Rust 1.77 and 1.78: The Changes That Happened to u128/i128
This story was originally published on HackerNoon at: https://hackernoon.com/rust-177-and-178-the-changes-that-happened-to-u128i128. …
2 months, 2 weeks ago

Definitive Guide to Multi-Threaded Rendering on the Web
This story was originally published on HackerNoon at: https://hackernoon.com/definitive-guide-to-multi-threaded-rendering-on-the-web. …
2 months, 2 weeks ago