Episode Details
Back to Episodes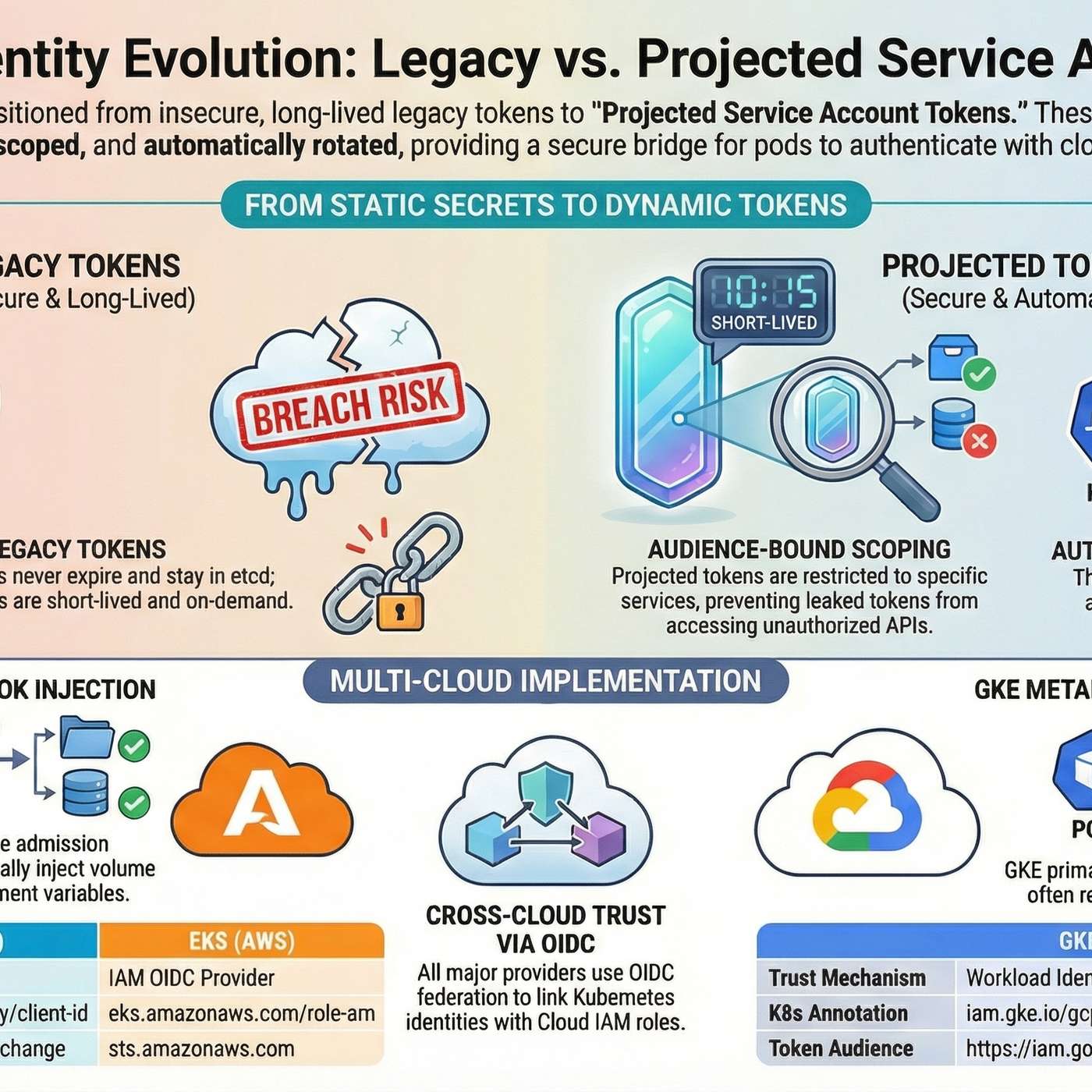
Secure Pod Identity Across Clouds: AKS Workload Identity, EKS IRSA, GKE Workload Identity
Description
This story was originally published on HackerNoon at: https://hackernoon.com/secure-pod-identity-across-clouds-aks-workload-identity-eks-irsa-gke-workload-identity.
Projected service account tokens bring expiration, rotation, and audience binding to Kubernetes pod auth.
Check more stories related to programming at: https://hackernoon.com/c/programming.
You can also check exclusive content about #kubernetes, #eks, #aks, #gke, #cloud, #credentials, #service-account-token-rotation, #projected-service-account, and more.
This story was written by: @pjajoo. Learn more about this writer by checking @pjajoo's about page,
and for more stories, please visit hackernoon.com.
Learn how Kubernetes projected service account tokens replace legacy secret-mounted tokens with short-lived, audience-scoped JWTs—plus how AKS, EKS (IRSA), and GKE use them for workload identity.