Podcast Episodes
Back to Search
Threat Hunting in the Cloud: Defending AWS, Azure and Other Cloud Platforms Against Cyberattacks
This Book is about threat hunting in cloud environments, specifically AWS and Azure. The authors, experienced cybersecurity professionals, present a …
1 year, 1 month ago
Threat Modeling: Designing for Security
This Book about threat modeling, a process for identifying and mitigating security risks in software. The book explains various threat modeling strat…
1 year, 1 month ago
Write Great Code, Volume 2, 2nd Edition: Thinking Low-Level, Writing High-Level
This Book is an excerpt from a Book on writing efficient high-level language (HLL) code by leveraging low-level understanding. It explores compiler o…
1 year, 1 month ago
Software Craftsman, The: Professionalism, Pragmatism, Pride
Sandro Mancuso's The Software Craftsman advocates for professionalism and pride in software development, contrasting outdated notions of seniority wi…
1 year, 1 month ago
The Shellcoder's Handbook: Discovering and Exploiting Security Holes
The provided Book is an excerpt from "The Shellcoder’s Handbook," a book detailing the exploitation of software security vulnerabilities. The book fo…
1 year, 1 month ago
The Quick Python Book, Second Edition
This Book is from the second edition of The Quick Python Book, a programming tutorial. The book covers fundamental Python concepts, including syntax,…
1 year, 1 month ago
The Pentester BluePrint: Starting a Career as an Ethical Hacker
"The Pentester Blueprint" is a guide to becoming an ethical hacker (pentester). The book covers the necessary technical skills, including operating s…
1 year, 1 month ago
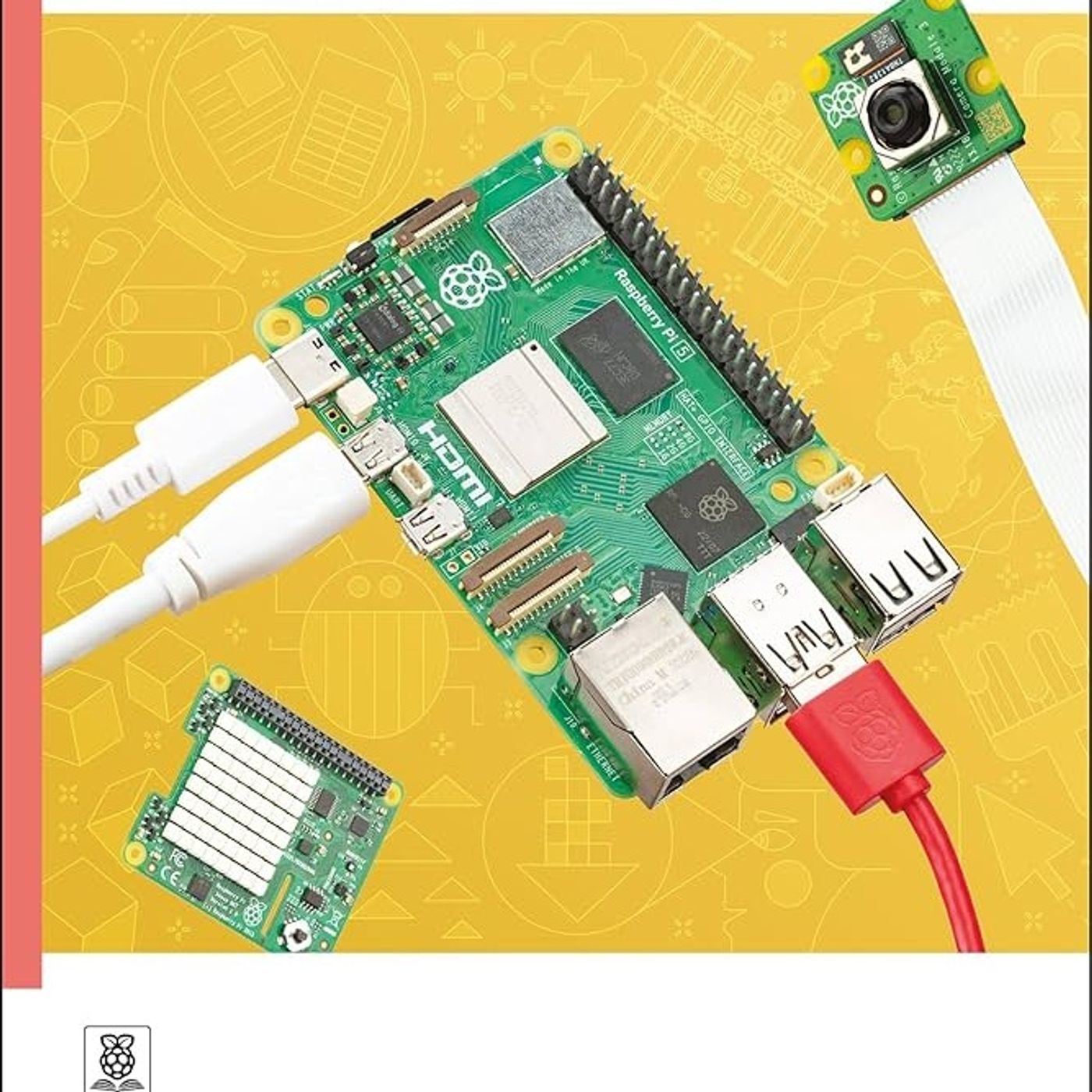
The Official Raspberry Pi Beginner's Guide: How to use your new computer
This Book provides a comprehensive introduction to the Raspberry Pi 4 Model B, covering its components, setup, and programming using Scratch and Pyth…
1 year, 1 month ago
The Official CompTIA Security+ Certification Study Guide
This Book is an excerpt from a CompTIA Security+ study guide that provides information about network security. The guide explores topics such as risk…
1 year, 1 month ago
The Linux Programming Interface: A Linux and UNIX System Programming Handbook
The provided Book is a collection of excerpts from Michael Kerrisk's "The Linux Programming Interface," a comprehensive guide to Linux and UNIX syste…
1 year, 1 month ago