Episode Details
Back to Episodes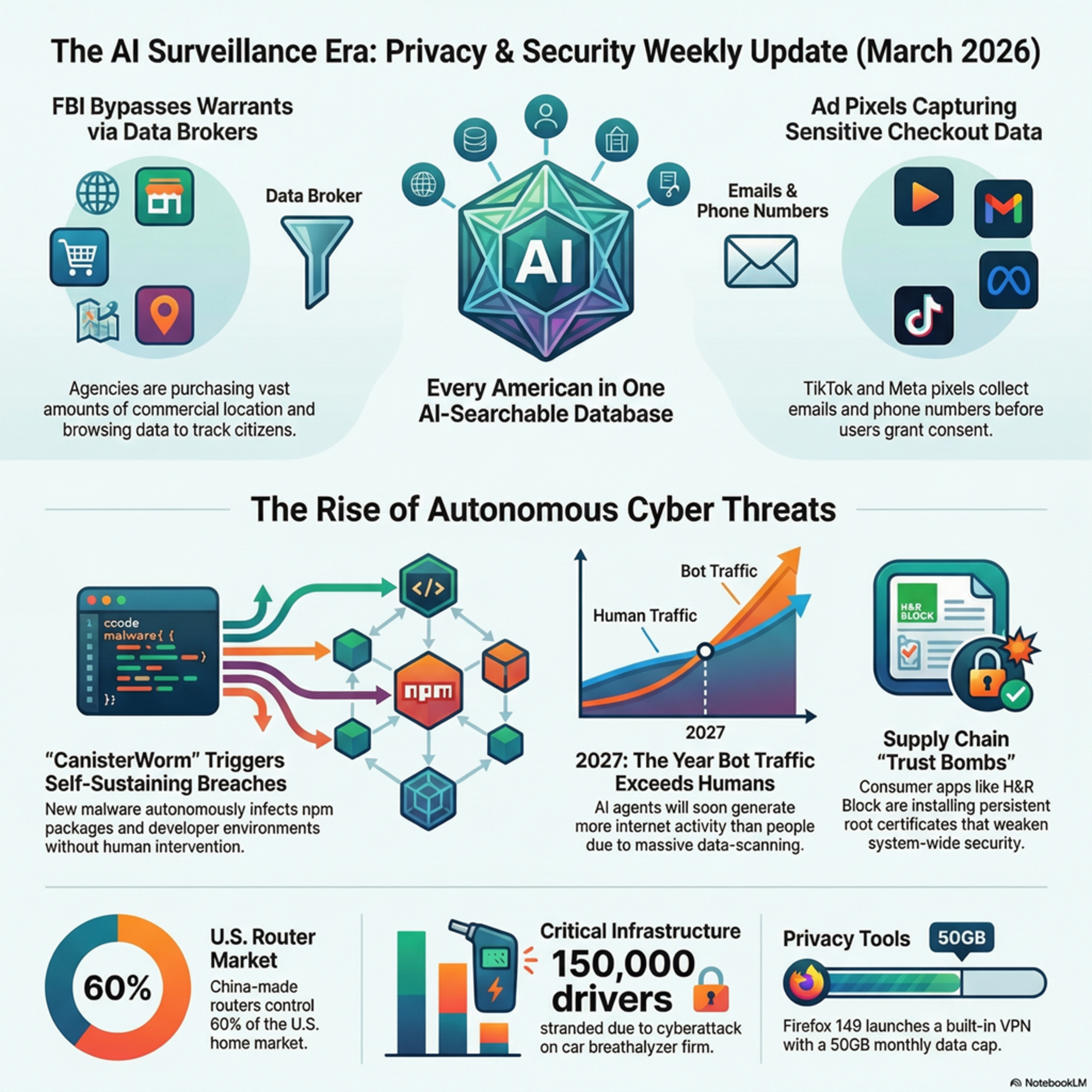
Episode 284.5. Deep Dive. Sold Out. The AI, Privacy, and Security Weekly Update for the week ending March 24th., 2026
Description
The technology landscape has shifted so profoundly that “IT risk” no longer captures current threats. This publication is now the AI, Privacy and Security Weekly Update, reflecting the reality that AI drives both innovation and adversary tactics. Episode 284 (week ending March 24, 2026) covers a surge of AI-driven developments, from autonomous malware to expanding federal data systems, marking the formal start of the surveillance era.
The New Surveillance Perimeter: Government Data Aggregation
A centralized AI “intelligence layer” is forming to map daily life with precision.
Federal Consolidation: Internal reports reveal a proposed U.S. system combining immigration, financial, and biometric data into an AI-searchable database.
Warrantless Access: FBI Director Kash Patel confirmed resumption of buying commercial location data from brokers.
The Upshot: This circumvents Fourth Amendment protections, enabling mass monitoring without individual warrants. The aggregation of sensitive datasets creates persistent “mission creep” and critical single points of failure for the software supply chain.
Autonomous Threats and Supply Chain Integrity
Adversaries now deploy self-propagating, automated infection loops that exploit development infrastructure.
CanisterWorm: Compromised credentials in Trivy propagated malware across 47 npm packages, harvesting tokens to spread autonomously.
Open-Source Sabotage: A related campaign weaponized open-source libraries to erase data on systems in Iran.
The Upshot: One stolen credential can now trigger a self-sustaining breach. Security strategy must extend beyond networks to verify every automated dependency.
Infrastructure Vulnerabilities and State Control
Connectivity itself is becoming a tool of control,and a potential systemic failure.
Strategic Disruption: Russia’s mobile internet outages illustrate “digital crackdowns.” Local businesses now lobby to restore access to foreign apps like Telegram and WhatsApp vital for global communication.
IoT Lockouts: A cyberattack on Intoxalock disabled 150,000 court-mandated breathalyzers, stranding drivers.
The Upshot: Cloud dependence in IoT and politically constrained connectivity expose how fragile digital infrastructure has become for both citizens and commerce.
Technological Shifts: Automation and Corporate Responsibility
By 2027, automated bot traffic will outpace human activity, forcing a transition from cybersecurity to automation management. Hardware like Intel’s “Heracles” chip increases Fully Homomorphic Encryption (FHE) speed 5,000-fold, enabling encrypted computation at scale.
Yet “trust bombs” persist:
H&R Block: Installed a root certificate (expiring 2049) with its private key embedded, allowing forged secure sites.
Bucketsquatting: AWS closed a loophole letting attackers hijack deleted S3 bucket names.
Privacy Push: The FCC banned new foreign-made routers over national security risks, and Mozilla introduced a 50GB/month VPN for Firefox to make privacy default.
The Upshot: As automated and AI-driven activity dominates the internet, privacy and trust have become core business imperatives,no longer optional features but essential components of market credibility.
We hope you enjoyed this week's update and look forward to sharing more AI, Privacy, and Security stories next week!