Episode Details
Back to Episodes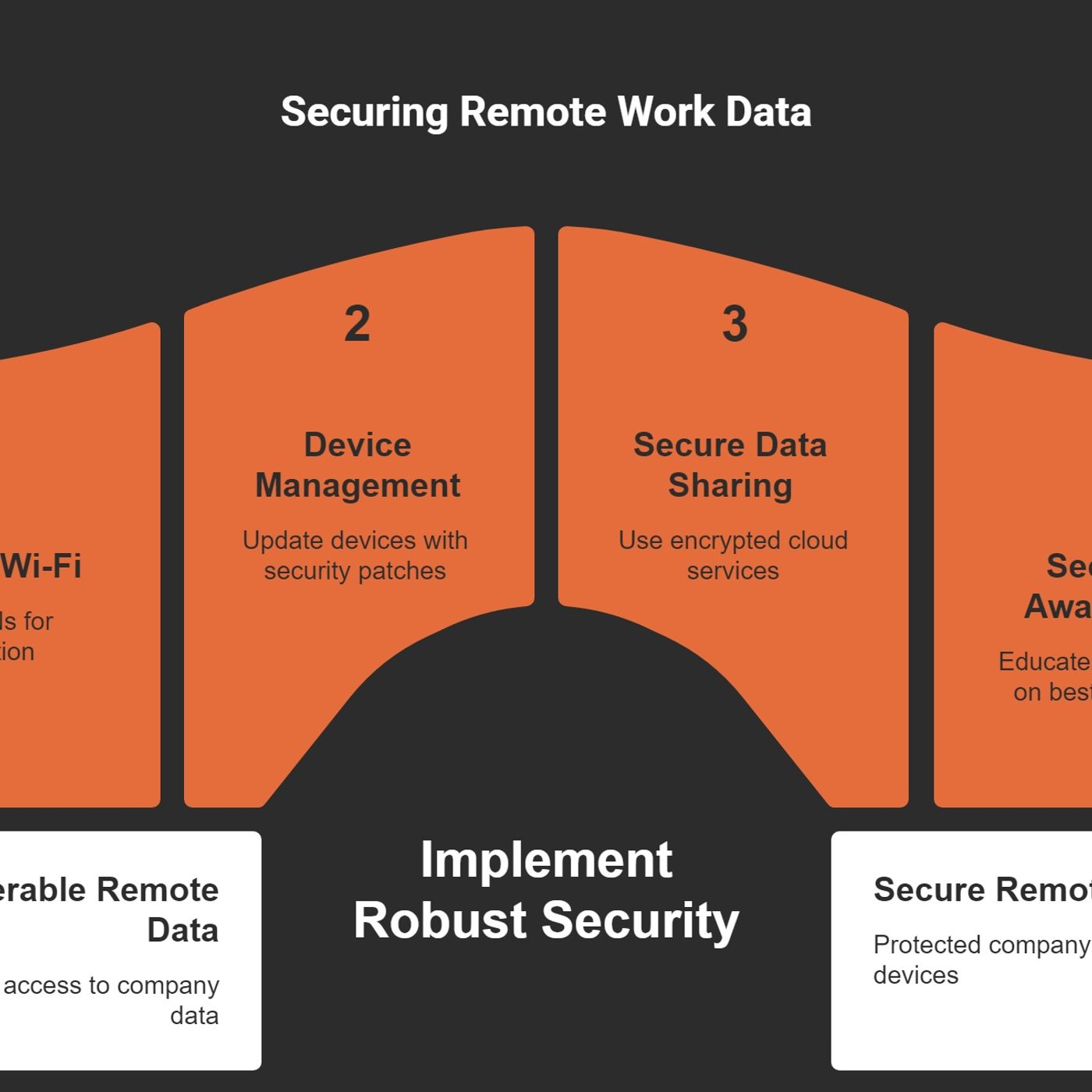
SC-900 Exam Prep Part 1/8: The Cyber Security Fundamentals
Published 9 months, 3 weeks ago
Description
When I first started navigating the world of IT security, I had an overwhelming sense of confusion. With the rise of cloud services and the shift to remote work, figuring out how to protect data felt like solving a puzzle without all the pieces. In this blog, we're unpacking the fundamentals of Microsoft Security, using insights from the SC-900 certification course to help those who are not only preparing for certification but anyone trying to understand just how deeply security and compliance touch our daily work lives.M365 Show is a reader-supported publication. To receive new posts and support my work, consider becoming a free or paid subscriber.The Necessity of Security in a Digital AgeIn today's world, security isn't just a tech issue—it's a vital business concern. Organizations are facing new challenges as we dive deeper into the digital age. A security breach can have dire consequences, not only financially but also in terms of customer trust and reputation. I want to explore these crucial aspects of digital security with you.Understanding the Financial Impacts of Security BreachesFirst, let's get real about the numbers. Did you know that the global cost of cybercrime is projected to reach $10 trillion by 2025? Think about that for a moment. That's a staggering amount, reflecting how serious these threats are. When a company experiences a data breach, the financial fallout can be devastating:* Immediate costs related to incident response.* Long-term reputational damage that can reduce customer trust.* Legal fees and potential fines from regulatory bodies.Now, imagine losing sensitive customer data...What would that cost your organization?This question isn’t just rhetorical; it’s a wake-up call for many businesses. If the financial implications aren’t convincing enough, the potential damage to your brand and customer loyalty should be.Why Trust is the Cornerstone of Customer RelationshipsTrust is paramount in any customer relationship. When customers share their information, they expect it to be protected. A breach shatters this trust. It's like a broken promise. Once lost, it’s incredibly challenging to rebuild.Companies that suffer data breaches often face severe reputational damage. According to studies, a significant percentage of organizations report losing customer trust after such incidents. Ironically, those companies that invest in security are more likely to earn customer loyalty. Therefore, investing in robust security measures isn’t just about compliance; it’s about protecting your most valuable asset—your customers.Rise of Cyber Threats in a Connected WorldAs we become increasingly interconnected, the rise of cyber threats remains alarming. From phishing attacks to ransomware, the landscape is constantly evolving. The pandemic accelerated the shift to remote work, opening more doors for cybercriminals. It's crucial to recognize that in this digital landscape, every endpoint can potentially be a vulnerability.We need to stay vigilant. Organizations should foster a culture of cybersecurity awareness. Training employees about the latest threats can be the first line of defense. Everyone plays a role in safeguarding the organization’s data.Real-World Examples of Data BreachesLet’s look at a few eye-opening examples. Companies like Equifax and Target have suffered massive data breaches, leading to millions of stolen records. The aftermath for these companies included hefty fines, legal battles, and plummeting stock prices. If they had prioritized security, could they have avoided this damage?These examples serve as a constant reminder: we can’t be complacent. Breaches aren't just headlines; they represent real people affected by the loss of their personal information.The False Sense of Security with Traditional PracticesMany businesses rely on outdated security practices, thinking they are safe. This assumption can be dangerous. Relying solely on firewalls and antivirus software isn’t enough anymore. Cyber threat