Episode Details
Back to Episodes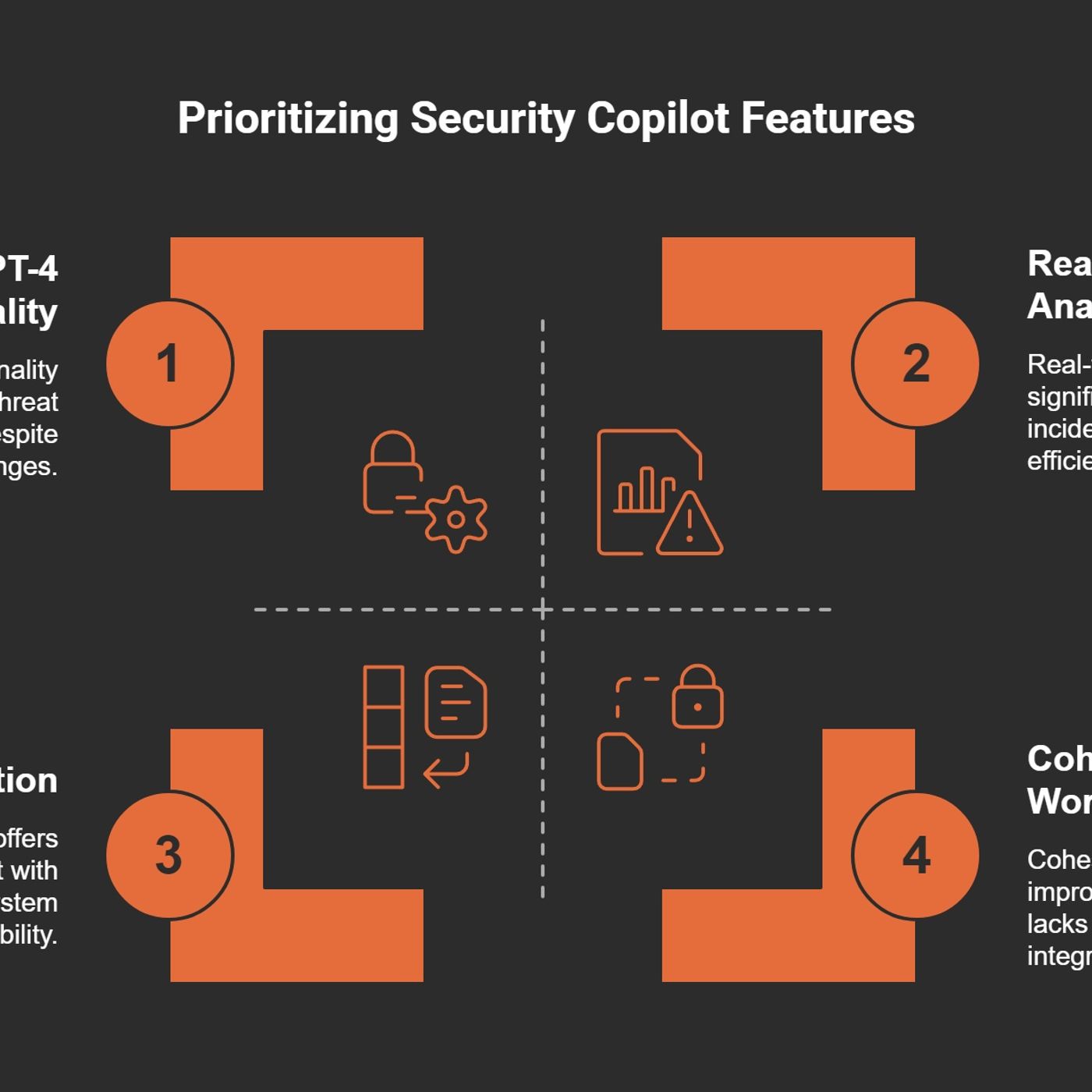
Microsoft Security Copilot in the SOC: cut alert overload, investigation time, and burnout with AI‑assisted incident response
Season 1
Published 1 year, 1 month ago
Description
(00:00:00) The alert overload challenge
(00:07:13) AI integration in security tools
(00:15:18) Contextual insights for threats
(00:27:47) Streamlined incident response
(00:37:57) Balancing security and usability
(00:59:59) Maximizing security Copilot value
Managing over 200 alerts before 9 AM is normal for many SOC analysts—and exactly why Microsoft Security Copilot matters. In this episode of M365.fm, Mirko Peters walks through what it actually feels like to chase incidents across 5–10 tools, bleed focus with every context switch, and spend 45 minutes on an investigation that AI can compress into 5.
He starts with the cognitive drain behind the dashboards. Jumping between Defender XDR, Entra, Sentinel, and ticketing systems turns every incident into a scavenger hunt, increasing the risk of missed clues and analyst burnout. Mirko uses a real Monday‑morning story—300 alerts, hours lost in tool‑hopping—to show how today’s SOC is less about a lack of data and more about too much of it, scattered across disconnected workflows.
From there he introduces Microsoft Security Copilot as the SOC’s AI sidekick, not a silver bullet. Copilot plugs into Defender, Entra, Intune and more, pulls context into one place, and uses GPT‑4 to summarize incidents, correlate signals, and generate investigation steps and response plans. Tasks that used to require manual log‑hunting become guided conversations: “Summarize this incident,” “What else is related?” or “Draft a response playbook,” turning 45‑minute investigations into 5‑minute, well‑documented sessions.
Mirko then focuses on incident response time. He explains how AI‑driven analytics help triage alerts, separate real threats from noise, and automate repetitive steps like enrichment and documentation so analysts can concentrate on high‑value judgment calls. Real‑world scenarios—suspicious logins, lateral movement, leaked credentials—show how Security Copilot can pre‑assemble evidence, propose containment actions, and feed structured reports back into existing SOC workflows instead of replacing them.
The episode closes on identity security and future SOC operating models. With more attacks targeting identities than endpoints, Mirko shows how Security Copilot can surface risky sign‑ins, permission misuse, and identity anomalies faster, helping teams treat identity as the true perimeter. The core message: Security Copilot will not do your job for you, but it can finally match the speed and complexity of modern threats—so your SOC spends less time drowning in alerts and more time actually containing attacks.
WHAT YOU WILL LEARN
(00:07:13) AI integration in security tools
(00:15:18) Contextual insights for threats
(00:27:47) Streamlined incident response
(00:37:57) Balancing security and usability
(00:59:59) Maximizing security Copilot value
Managing over 200 alerts before 9 AM is normal for many SOC analysts—and exactly why Microsoft Security Copilot matters. In this episode of M365.fm, Mirko Peters walks through what it actually feels like to chase incidents across 5–10 tools, bleed focus with every context switch, and spend 45 minutes on an investigation that AI can compress into 5.
He starts with the cognitive drain behind the dashboards. Jumping between Defender XDR, Entra, Sentinel, and ticketing systems turns every incident into a scavenger hunt, increasing the risk of missed clues and analyst burnout. Mirko uses a real Monday‑morning story—300 alerts, hours lost in tool‑hopping—to show how today’s SOC is less about a lack of data and more about too much of it, scattered across disconnected workflows.
From there he introduces Microsoft Security Copilot as the SOC’s AI sidekick, not a silver bullet. Copilot plugs into Defender, Entra, Intune and more, pulls context into one place, and uses GPT‑4 to summarize incidents, correlate signals, and generate investigation steps and response plans. Tasks that used to require manual log‑hunting become guided conversations: “Summarize this incident,” “What else is related?” or “Draft a response playbook,” turning 45‑minute investigations into 5‑minute, well‑documented sessions.
Mirko then focuses on incident response time. He explains how AI‑driven analytics help triage alerts, separate real threats from noise, and automate repetitive steps like enrichment and documentation so analysts can concentrate on high‑value judgment calls. Real‑world scenarios—suspicious logins, lateral movement, leaked credentials—show how Security Copilot can pre‑assemble evidence, propose containment actions, and feed structured reports back into existing SOC workflows instead of replacing them.
The episode closes on identity security and future SOC operating models. With more attacks targeting identities than endpoints, Mirko shows how Security Copilot can surface risky sign‑ins, permission misuse, and identity anomalies faster, helping teams treat identity as the true perimeter. The core message: Security Copilot will not do your job for you, but it can finally match the speed and complexity of modern threats—so your SOC spends less time drowning in alerts and more time actually containing attacks.
WHAT YOU WILL LEARN
- Why alert overload, tool‑hopping, and cognitive drain are the real SOC bottlenecks.
- How Microsoft Security Copilot integrates with Defender, Entra, and other tools to centralize context.
- How AI shrinks investigations from 45 minutes to 5 by summarizing, correlating, and guiding response.
- How automation and AI improve incident triage, documentation, and threat containment.
- Why identity s